HTTPS
HTTP and HTTPS
HTTP
- HTTP exchanges text, and HTML pages are also text.
- Because it sends and receives plain text rather than binary data, if someone intercepts signals on the network, the contents can be exposed. HTTPS was created to solve this security problem.
HTTPS
- HTTPS is a communication protocol in which the client and server exchange data using the SSL (Secure Socket Layer) protocol, which encrypts information on the Internet.
- HTTPS encrypts HTTP text.
- The S in HTTPS means Secure Socket, a secure communication network.
HTTPS Encryption Principle
The core principle of HTTP encryption is public key encryption.
- Certificates are issued so that messages are encrypted with a public key.
- Because encrypted messages can only be decrypted with the private key, no one in the middle can obtain the original data.
Characteristics of HTTPS
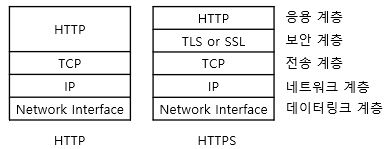
HTTPS implements HTTP on top of SSL/TLS.
Main functions
- Encryption
- Authentication
- Change detection and similar functions
URI Scheme prefix
- https
Port used
- If a URL has an
httpsURI scheme prefix instead ofhttp, it uses HTTPS port 443 rather than the usual HTTP port 80.
Standard
SSL/TLS
By using SSL (Secure Sockets Layer) or TLS (Transport Layer Security), which are encryption methods for HTTP communication, websites can be used safely.
SSL and TLS are essentially the same. SSL was invented by Netscape. As it became widely used and later came under the management of the IETF standards organization, its name changed to TLS. TLS 1.0 succeeds SSL 3.0, but the name SSL is still used much more commonly.
Structure for Securing HTTPS
SSL/TLS secures websites through the following three mechanisms.
Preventing Eavesdropping (Encrypted Communication)
Because website browsing passes through several servers, a third party can relatively easily intercept communication contents.
Even if data is intercepted, encrypting it before transmission prevents third parties from reading it.
Preventing Tampering
Message digests are used as a countermeasure against data tampering, such as rewriting product quantities in online shopping.
A message digest calculates a unique short value (hash value) from specific data. By comparing hash values when sending and receiving data, tampering can be detected.
Preventing Spoofing
By placing an electronic certificate called an SSL server certificate on the web server and verifying it at connection time, the identity of the website operator can be confirmed.
The certificate must be issued after authentication work by an approved certificate authority. If an untrusted certificate is used, a warning screen appears in the web browser.
How HTTPS Security Works
When a client (web browser) receives a URL with an https scheme rather than plain http, it opens a TCP connection to port 443 instead of port 80 on the web server and exchanges several security parameters in binary format (handshake, key exchange). Then the related HTTPS commands are executed.
HTTPS Exchange
To start HTTPS communication, four main phases are exchanged.
- Decide the encryption method
There are many encryption methods, so the web browser and web server must decide on an encryption method that both can use. The TLS version and message digest method are also decided at the same time. - Prove the communication partner
The browser checks with the SSL server certificate whether the web server is the correct target. If it cannot verify this, a warning is displayed. - Key exchange
The “key” used for data transmission is exchanged. The key is used for encryption during transmission and decryption during reading. - Confirm the encryption method
The final confirmation of the encryption method actually used is performed. When this step is complete, encrypted communication begins.
These four stages in HTTPS are called the SSL/TLS handshake.
HTTPS Server Certificate
A server certificate is an electronic certificate issued by a certificate authority to perform encrypted communication between a server and client.
It is based on X.509, and website information is added to the certificate.
Main Fields Included in a Server Certificate
- Certificate serial number and validity period
- Website name
- Website DNS host name (FQDN)
- Website public key
- Name of the signing authority (certificate authority)
- Digital signature of the signing authority
Main Certificate Checks for Website Information
- Date check
- Checks certificate validity period, expiration, activation, and similar status.
- Signer validity check
- Checks whether the certificate was derived from a valid certificate authority (chain of trust).
- Signature check
- Checks certificate integrity.
- Site identity check
- Checks whether the domain name specified in the certificate matches the actual domain name.
- Virtual hosting check
- When multiple sites or hosts are operated on one server, additional management and procedures are required.
References
- HTTPS Secure Hypertext Transfer Protocol HTTP security layer implementation
- HTTPS and SSL certificates | OpenTutorials